Data’s value is increasing‚ driving collaboration; DSAs are vital for secure‚ legal exchange‚ mirroring trends in data science and data management practices.
The Growing Need for Data Sharing
Data-driven decision-making is no longer a competitive advantage‚ but a necessity. Organizations across all sectors increasingly recognize the immense potential locked within their data silos. However‚ realizing this potential often requires combining datasets from multiple sources – necessitating robust data sharing practices. This need is amplified by advancements in fields like data science‚ data analysis‚ and data engineering‚ all reliant on access to comprehensive data.
The demand stems from diverse applications‚ including collaborative research‚ improved healthcare outcomes‚ enhanced business intelligence‚ and the development of innovative products and services. Furthermore‚ regulatory pressures‚ such as those related to open data initiatives‚ are also driving the need for formalized data sharing agreements. The proliferation of data‚ coupled with the complexity of modern data landscapes‚ underscores the critical importance of establishing clear guidelines and protocols for responsible data exchange.
What is a Data Sharing Agreement (DSA)?
A Data Sharing Agreement (DSA) is a legally binding contract outlining the terms and conditions under which data is exchanged between two or more parties. It’s a crucial document for establishing trust and ensuring responsible data handling. Unlike simple data use agreements‚ a DSA comprehensively addresses aspects like permitted uses‚ security protocols‚ ownership‚ and liability.
Essentially‚ it defines “who” can access “what” data‚ “how” it can be used‚ and “for how long”. A well-crafted DSA mitigates risks associated with data breaches‚ misuse‚ and non-compliance with relevant regulations like GDPR or HIPAA. It’s a cornerstone of ethical data practices‚ particularly as data science and data engineering become increasingly prevalent‚ demanding secure and governed data flows.

Key Components of a Data Sharing Agreement
DSAs require clear definitions of parties‚ data scope‚ permitted uses‚ security measures‚ ownership rights‚ and termination procedures for legally sound data exchange.
Defining the Parties Involved
Precisely identifying all parties – the data provider and data recipient – is foundational. This section must detail legal names‚ addresses‚ and designated representatives with authority to bind the organization; Consider including organizational structures‚ clarifying if entities are governmental‚ private‚ or academic.
Furthermore‚ specify the roles and responsibilities of each party concerning the data. For instance‚ the provider outlines data quality assurances‚ while the recipient commits to adhering to usage restrictions.
Clearly defining these roles minimizes ambiguity and establishes accountability. The agreement should also address potential subcontractors or affiliates who may gain access to the data‚ requiring explicit consent and extending obligations to them. Accurate party identification is crucial for enforcing the agreement and resolving disputes.
Scope of Data Shared – Specificity is Crucial
Ambiguity in defining the data’s scope invites legal challenges. The agreement must meticulously list the specific data elements‚ formats‚ and sources included. Avoid vague terms like “customer information”; instead‚ specify “names‚ addresses‚ email addresses‚ and purchase history.”
Detailing data fields‚ databases‚ or files is essential; Consider including data dictionaries or appendices for clarity.
Furthermore‚ explicitly state what data is excluded from the agreement. This prevents unintentional sharing of sensitive information. The agreement should also address how data will be updated or refreshed‚ and the frequency of such updates. Precise scope definition ensures both parties understand exactly what is being shared‚ minimizing risk and maximizing the agreement’s effectiveness.
Permitted Uses of the Data
Clearly outlining permitted uses is paramount. The DSA must explicitly state how the receiving party can utilize the shared data. For example‚ is it solely for analytical purposes‚ or can it be used for marketing campaigns?
Restrictions should be detailed – prohibiting resale‚ commercial exploitation‚ or use for competitive purposes.
Specify if the receiving party can combine the data with other datasets‚ and under what conditions. Any intended data analysis‚ including the creation of derivative works‚ requires explicit permission.
Furthermore‚ the agreement should address whether the receiving party can publish or present findings based on the data‚ and if so‚ whether anonymization or aggregation is required. Precise limitations safeguard the data provider’s interests.

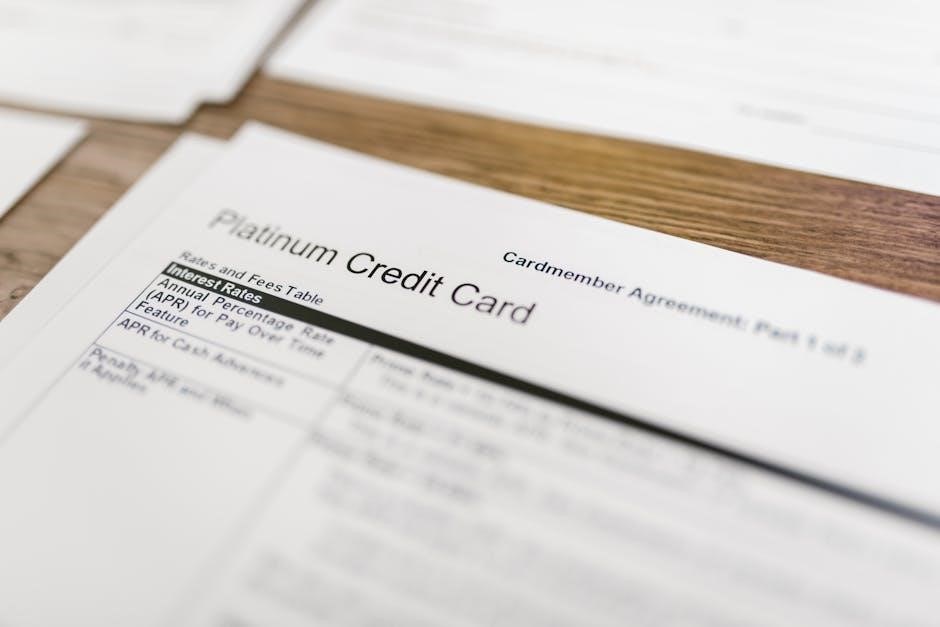
Legal and Regulatory Considerations
Compliance with GDPR‚ HIPAA‚ and data residency laws is crucial; DSAs must address these‚ ensuring lawful data handling and transfer protocols.
GDPR and Data Protection Regulations
Data sharing agreements must meticulously align with the General Data Protection Regulation (GDPR) principles. This necessitates clearly defining the legal basis for processing‚ whether consent‚ contract‚ or legitimate interests. The agreement should detail how data subjects’ rights – access‚ rectification‚ erasure‚ and data portability – will be honored.
Specific provisions addressing data minimization‚ purpose limitation‚ and storage limitation are essential. Furthermore‚ the agreement must outline procedures for handling data breaches‚ including notification timelines to supervisory authorities and affected individuals‚ as mandated by GDPR.
Cross-border data transfers require careful consideration‚ particularly concerning adequacy decisions or appropriate safeguards like Standard Contractual Clauses (SCCs). Demonstrating accountability through data protection impact assessments (DPIAs) may also be necessary‚ especially when high-risk processing is involved. Regular audits and updates to the DSA are vital to maintain ongoing compliance.
HIPAA Compliance (If Applicable)
If the data shared includes Protected Health Information (PHI)‚ strict adherence to the Health Insurance Portability and Accountability Act (HIPAA) is paramount. The Data Sharing Agreement (DSA) must designate each party as either a Covered Entity or a Business Associate‚ defining their respective responsibilities.
The DSA needs to detail permitted uses and disclosures of PHI‚ limited to those necessary for the specified purpose. It must incorporate HIPAA’s Security Rule requirements‚ addressing administrative‚ physical‚ and technical safeguards to protect data confidentiality‚ integrity‚ and availability.
Breach notification protocols‚ exceeding GDPR timelines‚ are crucial‚ alongside provisions for data subject access rights under HIPAA. Regular audits and compliance assessments are essential. The agreement should also outline procedures for data return or destruction upon termination‚ ensuring complete PHI removal‚ and demonstrate ongoing compliance with evolving HIPAA regulations.
Data Residency and Transfer Restrictions
Data Residency clauses within the DSA specify the geographic location where shared data must be stored and processed. This is critical given increasing global data protection laws. Restrictions on data transfer are vital‚ particularly when crossing international borders‚ impacting compliance with regulations like GDPR.
The agreement must clearly define permitted transfer mechanisms – such as Standard Contractual Clauses (SCCs) or Binding Corporate Rules (BCRs) – ensuring adequate data protection levels in the recipient’s jurisdiction.
Considerations include potential government access requests and differing legal frameworks. The DSA should address scenarios involving sub-processors‚ outlining their compliance obligations. Regularly review and update these clauses to reflect evolving legal landscapes and ensure continued lawful data handling‚ especially concerning cross-border data flows.

Data Security and Confidentiality Clauses
DSAs necessitate robust security protocols – encryption‚ access controls – and detailed breach notification procedures‚ safeguarding sensitive data against unauthorized access or disclosure.
Data Encryption and Access Controls
Data encryption‚ both in transit and at rest‚ forms a cornerstone of DSA security. Agreements should specify encryption standards – such as AES-256 – and key management protocols. Access controls are equally vital‚ limiting data access to authorized personnel only‚ based on the principle of least privilege.
Detailed access logs and audit trails are essential for monitoring data usage and detecting potential breaches. Multi-factor authentication should be implemented wherever possible‚ adding an extra layer of security. The DSA must clearly define roles and responsibilities regarding data access‚ outlining who can view‚ modify‚ or delete data‚ and under what circumstances. Regular security assessments and penetration testing are recommended to identify and address vulnerabilities. Furthermore‚ the agreement should address the secure disposal of encryption keys and access credentials when the agreement terminates.
Breach Notification Procedures
Data sharing agreements must meticulously outline breach notification procedures. A clear timeline for notification is crucial – typically within 72 hours of discovery‚ aligning with GDPR requirements. The DSA should specify who must be notified: the data-sharing partner‚ relevant regulatory bodies‚ and potentially affected individuals.
The notification must detail the nature of the breach‚ the types of data compromised‚ the potential impact‚ and the steps taken to mitigate the damage. A designated point of contact for breach-related communication should be established. Agreements should also address the costs associated with breach response‚ including forensic investigations‚ legal fees‚ and credit monitoring services. Regular testing of breach response plans is vital to ensure effectiveness and compliance. Documentation of all breach-related activities is essential for legal and regulatory purposes.

Confidentiality Obligations
Data sharing agreements necessitate robust confidentiality clauses. Both parties must commit to protecting the shared data from unauthorized access‚ use‚ or disclosure. This includes implementing appropriate security measures – encryption‚ access controls – and restricting access to personnel with a legitimate need to know. The DSA should define “Confidential Information” broadly‚ encompassing all shared data and related materials.

Obligations should extend beyond the term of the agreement‚ potentially including post-termination confidentiality requirements. Exceptions may exist for legal obligations or court orders‚ but these should be clearly defined. Agreements often include provisions prohibiting reverse engineering or attempts to de-identify data without explicit consent. Regular audits and compliance checks can help ensure adherence to confidentiality obligations‚ safeguarding sensitive information.
Ownership and Intellectual Property Rights
DSAs must clarify data ownership and intellectual property stemming from analysis; agreements should address rights to insights and derivative works clearly.
Data Ownership Clarification
A crucial element within any robust Data Sharing Agreement (DSA) is a precise clarification of data ownership. The agreement must explicitly state who retains ownership of the data being shared – is it the providing party‚ the receiving party‚ or a jointly held arrangement? This isn’t merely a legal formality; it dictates control over usage‚ modification‚ and future distribution.
Often‚ the original data provider retains ownership‚ granting the recipient a license to use the data under specific conditions. Conversely‚ if the recipient significantly transforms the data‚ creating new datasets or insights‚ ownership of those derived products may shift. The DSA should detail these scenarios.
Ambiguity here can lead to disputes‚ hindering collaboration and potentially violating intellectual property rights. Clear language defining ownership‚ usage rights‚ and any limitations is paramount for a successful and legally sound data sharing partnership. Consider referencing DUNS numbers for entity identification.
Intellectual Property Rights Regarding Data Analysis
Data analysis performed on shared data frequently generates new intellectual property (IP). A comprehensive Data Sharing Agreement (DSA) must address ownership of these analytical outputs. Does the original data owner retain rights to insights derived from their data‚ or does the analyzing party gain ownership? This depends on the level of transformation and originality.
If the analysis is largely automated or uses pre-existing algorithms‚ the data provider may retain IP rights. However‚ if the analysis involves substantial creative effort and novel methodologies – akin to qualitative data analysis with tools like Atlas.ti – the analyzing party may claim ownership.
The DSA should specify licensing terms for analytical results‚ including rights to publish‚ patent‚ or commercialize. Clear delineation prevents disputes and encourages innovation‚ fostering a collaborative environment while protecting the interests of all parties involved.

Agreement Termination and Data Return/Destruction
DSAs outline conditions for termination and mandate secure data handling—either its return to the owner or certified‚ complete destruction‚ safeguarding confidentiality.
Termination Clauses and Conditions
Data sharing agreements (DSAs) must clearly define circumstances allowing termination. These typically include material breaches of the agreement – such as unauthorized data use or security failures – and instances where the purpose of data sharing is no longer valid.
Clauses should specify notice periods required for termination‚ ranging from 30 to 90 days‚ allowing parties time to adjust. Unilateral termination rights‚ permitting one party to end the agreement at will‚ are often limited and may require substantial justification.
Furthermore‚ provisions addressing the ongoing obligations post-termination are crucial. This includes stipulations regarding the continued confidentiality of data‚ procedures for data return or destruction‚ and potential liabilities arising from data misuse before termination. Clearly defined conditions minimize disputes and ensure responsible data handling even after the agreement ends.
Procedures for Data Return or Secure Destruction
Data sharing agreements (DSAs) necessitate detailed protocols for handling data upon termination or request. These procedures must outline whether data will be returned to the originating party or securely destroyed. If returned‚ the DSA should specify the format and method of transfer‚ ensuring data integrity and confidentiality during transit.
For secure destruction‚ the agreement should mandate adherence to industry-standard methods‚ such as cryptographic erasure or physical destruction of storage media. Documentation confirming complete data removal is essential.
Furthermore‚ the DSA should address residual copies or backups‚ requiring their deletion or anonymization. Clear timelines for completion of these procedures‚ typically within 30-60 days‚ are vital. These provisions safeguard sensitive information and demonstrate responsible data governance.